Server Fingerprints
Secure servers will frequently use security fingerprints to identify themselves. When a client connects, the server presents a fingerprint and this gives the client a chance to disconnect before sending through more sensitive details like username and password.
When LogViewPlus first connects to a secure server, it has nothing to compare the fingerprint against. The default behavior in this scenario is that LogViewPlus will assume the fingerprint is valid. We take a slightly less secure approach here in favor of usability because we believe that most connections will be made behind a firewall where the initial connection can be trusted. If you would like to verify the fingerprint before connecting, we recommend using a 3rd party tool (such as Putty) immediately before the initial connection attempt. Alternatively, you can set the Lockdown property to true in %ProgramFiles%\LogViewPlus\LogViewPlus.exe.config.
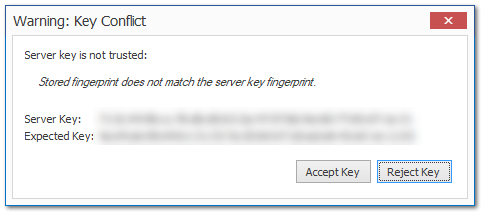
Regardless of the security model used, once the initial connection has been made the fingerprint of the server will be permanently cached. On future connection attempts, the cached fingerprint will be compared against the fingerprint presented. If a discrepancy is found, the user will be presented with a dialog giving the option to accept or reject the key. If the key is rejected, then the connection will be terminated and no credentials will be sent.